Free Assessment
For new clients, we are offering a no-obligation health assessment of your computer network and business technology. We will analyze your network to identify vulnerabilities that could leave your organization at risk of a business interruption. Depending on what we uncover, we will also make suggestions on ways to prevent unauthorized access, augment security systems, better lock down sensitive data, become more mobile and, in general, get more out of your existing technology infrastructure.
You will receive our Client Risk Report, a 6 to 8 page Executive Summary that provides an overview of the devices on the network along with a network Risk Score and analysis of each potential issue we uncover. We will review this document with you, discuss the findings in detail, and answer any questions you may have.
It’s a $1,000.00 value, offered at no cost to qualifying organizations.
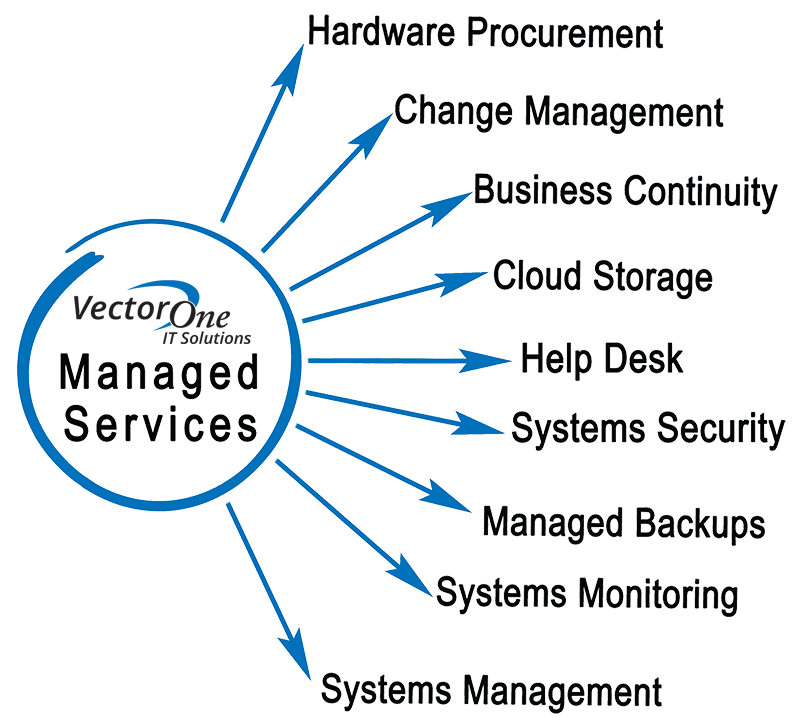
Managed Services
For our managed service clients, we become your IT department for a fixed monthly price. No surprise bills, we “take ownership” for your IT environment, taking care of everything in your network… users, too! Let us focus on your IT, so you can focus on your business.
What’s included? We tailor our managed service offering to each client’s individual needs, which may include some or all of the following:
- Remote monitoring and alerting for all servers, workstations, and network devices
- Unlimited support and administration
- Help desk
- Backup
- Network Security
- Cloud / subscription services
We also offer “hybrid managed services,” where we provide all of the same services at hourly rates.
Professional Services
Sometimes you just need some supplemental expertise for a particular project that you may not have time for, or you just need it done right the first time. We’ll work with you or your IT staff on an hourly or fixed-cost project basis. Typical project engagements might include:
- Strategic IT consulting
- Server, workstation, or application deployment
- Upgrades, migrations, or consolidations
- Virtualization
- Troubleshooting and remediation
- and more!
Cloud Services
By “the cloud”, we mean any externally hosted service or application, typically on a subscription basis. Some solutions leverage both on-premise and “in the cloud” components to best meet your needs. Offerings include:
- Proactive monitoring and alerting
- Backup and disaster recovery
- Cybersecurity
- Hosted email / MS Exchange
- IP Telephony / VoIP
- Antivirus / malware protection
- File sharing and synchronization
Security & Network Integrity
Network integrity is a broad term, going beyond just security, to include:
- Security
- Availability
- Performance
- Recoverability
We leverage multiple tools and products to create a customized defense-in-depth strategy that is “right-sized” to your needs and budget, which might include:
- Antivirus
- Application Whitelisting
- Backup and rapid recovery
- Centralized administration
- Clustering for high availability
- Cyber Insurance
- Encryption
- Firewalls with advanced security features
- Intrusion prevention
- Mail filtering
- Monitoring and alerting
- Password management
- Patching / updating
- Performance tuning
- Policy development
- Redundancy for critical components
- User training
- Vulnerability assessment
- Web filtering
- Wireless security
Backup & Disaster Recovery
Your number one defense against data loss is the performance of regular backups. What causes data loss?
- Systems failure
- User error
- Malicious users
- Malicious software, especially ransomware
- Fire, flood, locusts! OK… maybe not locusts.
Not all backups are equal, and it’s not one size fits all. We’ll design and implement a backup solution appropriate to your needs, which might include:
- Backup for servers and databases
- Backup for desktops and laptops
- Backup for cloud data, like MS Office 365
- Rapid recovery
- Disaster recovery “in the cloud” or at a secondary site of your own
Work From Home
We work with our clients to determine the best solutions to help them work from home, on the road… anywhere! Work-from-home solutions might include any or all of:
- Terminal services
- Virtual Private Networking (VPN)
- Desktop remote control
- File synchronization
Cyber Insurance
Cyber insurance can be complicated, which is why Vector One has teamed up with Zeguro to simplify purchasing cyber insurance for you so you can make the most informed decision about your cyber insurance needs. Zeguro Cyber Insurance provides comprehensive coverage so your organization can meet contractual requirements and continue to thrive with minimal disruption should a data breach occur.
Partners & Procurement
Vector One partners with leading information technology vendors, manufacturers, and distributors. We leverage our partnerships to get you the right products at the right price, including from: